Component has been implemented to be able to to anonymize, pseudonymize and generate data in databases.
This component gives the capability to companies to be GDPR (General Data Protection Regulation) compliance.
You will find in this getting started article the first steps to start working with Sampling Component.
You can also refer to Stambia DI for Privacy Protect article for further information about supported operations, download page, and more.
Prerequisites:
- Stambia DI Designer / Runtime 20.3.0 or higher
- Component Base 2.0.6 or higher
Note:
Stambia DI is a flexible and agile solution. It can be quickly adapted to your needs.
If you have any question, any feature request or any issue, do not hesitate to contact us.
This component may require a dedicated license.
Please contact the Stambia support team if you have any doubt and if you need to use it in a production environment.
Component Installation
Install Privacy Protect Component as any other Stambia Component.
Refer to the Stambia DI for Privacy Protect article for the download section.
Once the installation is performed, you can continue to the next step.
Privacy Protect reference project installation
Privacy Protect needs a reference project to load, particularly, standard dictionaries prepared and made available inside this Component.
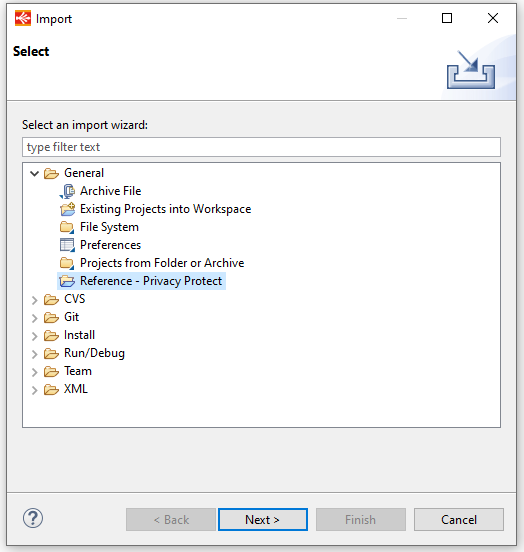
To import Privacy Protect Reference project, right click and «Import» in the project explorer, then select «Reference - Privacy Protect» in «General» folder and confirm the name of the reference project after pushing the Next button.
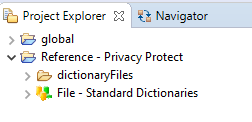
Privacy Protect reference project is created:
Privacy Protect methods
Different methods are available in Privacy Protect.
To apply the best protection on your data, you must choose the better method for each of your columns, depending on each data itself and on your business and technical context
Substitution with standard dictionary
It is possible to substitute your personal values to protect by values contained in dictionary tables.
Indeed, Privacy Protect Component is shipped with some standard dictionaries. Those dictionaries can have several properties/columns.
Those dictionaries must be integrated in your database with «Load Standard dictionaries» tool in advance.</>p
Substitution with custom dictionary
With «Substitution with custom dictionary», Privacy Protect allows you to build and use your own dictionary and compute the population with each term retrieved.
You must give a name to each custom dictionary and use it directly on the same field or after in another field.
Deduction from standard dictionary
It is also possible to deduct some properties from «Standard dictionaries» when they are built with additional properties, like gender for the firstname or sector and email_suffix for company dictionaries.
Random generation
Another way to modify/generate values is to choose the random generation method.
It must be required to drive the way to generate random data through the Random generation type
Text generation
Instead of random characters generation, it’s possible to generate one or several sentences, when columns need to be substituted or completed (row generation) with sentences.
Text generation build random sentences in the language corresponding to the chosen geographic coverage (if any) or in the following languages: French, Spanish, Italian, German, English.
Sequence generation
Sequence generation allows to generate a sequence of number.
This functionality could be useful to complete technical internal identifier.
You must specify the Start value and the Increment value: Start value and Increment value can be decimal values and Increment value can be a negative value.
Obfuscation
Obfuscation allows to hide/transform a part of a column value: it’s often used to display partially a credit card number for example!
Deletion
Deletion allows simply to delete the column value: it’s a method to use when a field is not required to be kept.
Java transformation
«Java transformation» method allows to implement more complex transformation rules adding Java programming capabilities.
Encryption
Encryption can be used to protect data: It implements «Java encryption» capabilities, with two encryption types and different encryption algorithms, mode and padding and with a key type to define.
Correspondence table
A correspondence table must be used to replace each original value into the same target value. It can be used in several locations/columns.
Anonym virtual column
Anonym virtual columns allow to produce intermediate transformation before using those virtual columns in the specification of a «real» column to protect.
Those virtual columns do not need to be added as a dependency with other columns for the real column and are not generated on target tables.
You can find examples of differents methods, in the Reference documentation of the Privacy Protect Component, in Stambia DI.
In the Menu "Help" / "Help Contents":

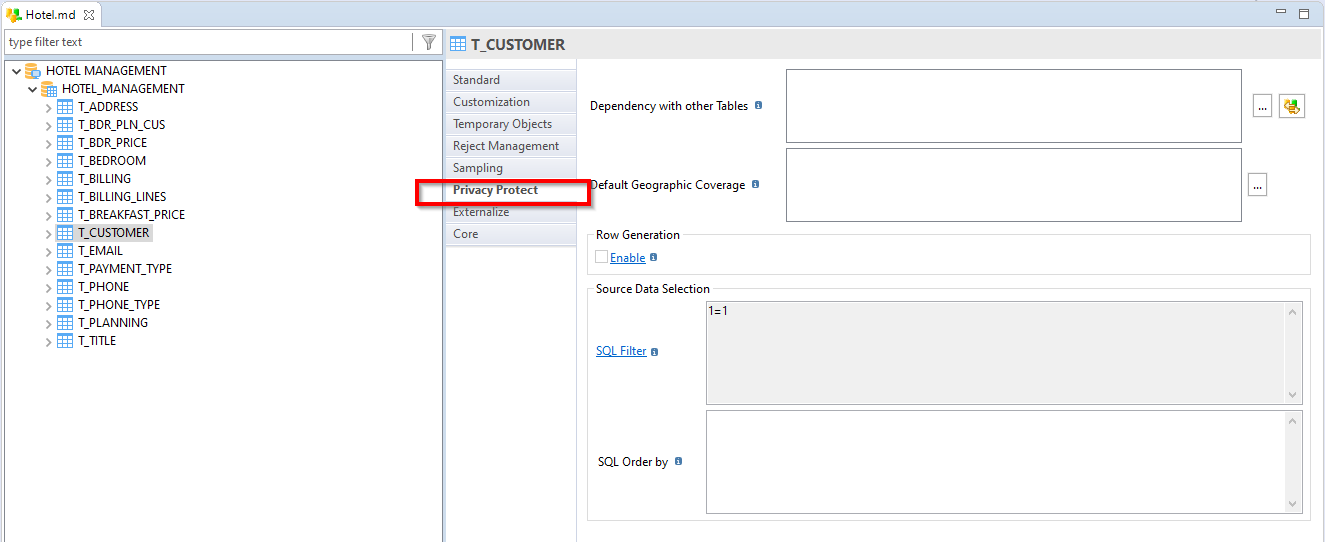
Privacy Protect usage
To drive Personal Data protection in Privacy Protect, you must parametrize the tool at 3 levels in Metadata properties of a database, using the «Privacy Protect» view.
You can find all the configurations to set, in the Reference documentation of the Privacy Protect Documentation, in Stambia DI.
Privacy Protect tools usage
Privacy Protect Component provides several tools.
Data catalog tool
Data catalog tool allows to share the list of protected data with all the actors involved before applying the protection and giving availability to authorized users.
Load Standard Dictionary tool
Standard dictionaries need to be initialized (loaded) if you use them.
Privacy Protect tool
Privacy Protect tool applies all the protection methods defined in the metadata of the source schema and integrate them in the target schema.
You can find informations about the tools,in the Reference documentation of the Privacy Protect Documentation, in Stambia DI.


